Shield OnPremise · 10 Gbps
Behind the Firewall. Before the Threat.
Hardware appliance for the data center and OT environments. Bi-directional enforcement at the connection layer. No agent. No baseline. No wait.







There's Bad Traffic Trying to Reach Your Network Right Now.
Shield OnPremise blocks it at the connection layer. Take a tour below.
Shield OnPremise Blocks What Shouldn't Be There.
Powered by the Global Threat Engine, Shield OnPremise sits behind your firewall. Trusted connections are permitted. Malicious connections are blocked in-line, both directions, at 10 Gbps. No alerts to chase.






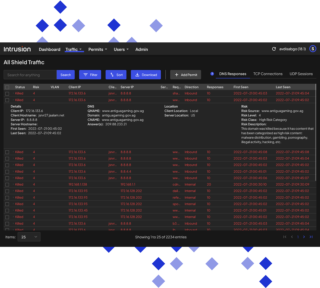
Every Inbound and Outbound Block. In Real Time.
The full event log of every connection Shield blocked. Drill down on any single block to see why: source, destination, direction, risk classification. Export to CSV or Excel when you need to share.







See Where Your Network Is Talking. And Who To.
An interactive map of every country your network is sending traffic to or receiving traffic from. Spot the geographies that shouldn't be in your picture. Use it for compliance reporting, incident review, or routine hygiene.





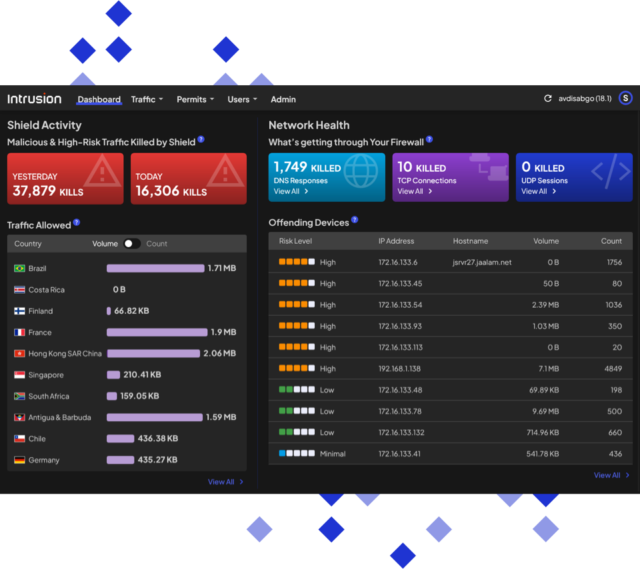
Find the Devices Calling the Wrong Neighborhoods.
Which devices on your network are racking up the most blocked outbound connections? Shield surfaces them so you can prioritize patching, isolation, or replacement.
Rack Space, Meet Backbone.
Shield OnPremise gives your network a prevention-first layer that actually knows when traffic has bad intentions.
Less Reacting. More Protecting.







See Every Connection.
If an IP is trying to reach your network, Shield sees it. Real-time, bi-directional, no sampling. Full visibility of every connection being made on your network.

Know the Good From the Bad. Automatically.
Stop guessing. The Global Threat Engine knows. 25 years of historical IP and DNS reputation, 8.5 billion combinations, all in one decision engine. Shield classifies the connection and acts on it without waiting for human input.







Protect Your Network and Your Team.
No alerts to triage. No incident response queues. Shield blocks the connection autonomously and your team works on the issues that actually need humans.

Harder for Zero Days to Land.
Most stacks don't have enough historical reputation data to classify a connection they've never seen. Shield does. 25 years of IP and DNS history means new threats often connect to infrastructure with a known-bad history, and Shield blocks them on the reputation alone.







Strengthen the Stack You Already Have.
Shield sits behind your firewall and works with what you've got. SIEM, SOAR, EDR, NDR. None of them have to change. On day one Shield makes the rest of your stack work better. Over time, it can take the place of some of them.
What Customers Are Saying.













